In today’s revolutionizing era, the integration of generative AI has become crucial for more productive, accessible, and personalized patient care. In this blog, we will discover the transformative impact of generative AI on healthcare, exploring its application, advantages, and probability. With a center on healthcare app development and healthcare software development, we’ll examine how these advances help the healthcare division accomplish way better results.
What Is Generative AI?
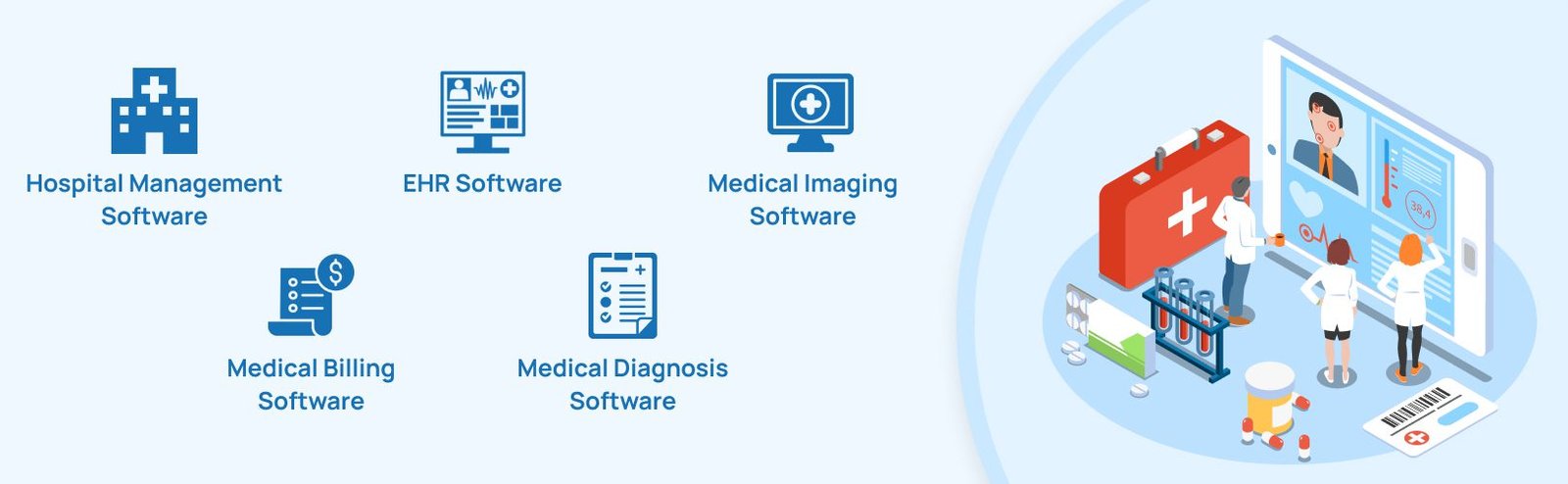
Generative AI alludes to fake insights frameworks able to create modern substance, such as content, pictures, or sound, based on the information they have been prepared on. Unlike conventional AI, which depends on foreordained rules and designs, generative AI employs machine learning models to make unequivocally modified yields. In healthcare, this implies creating arrangements that can analyze complex datasets, give bits of knowledge, and recommend medications. Further, generative AI can be incorporated easily with the assistance of EHR software development.
Generative AI Provides Custom Healthcare Solutions!
Diagnostic Assistance
Generative AI exceeds expectations in diagnostic help by analyzing restorative images, lab results, and patient histories. It can more precisely identify peculiarities in X-rays, MRIs, and CT scans than human eyes. By identifying patterns and correlations that human specialists can miss, generative AI ensures earlier and more precise diagnoses. This capability is especially beneficial in radiology and pathology, where accuracy is crucial.
Personalized Treatment Plans
Healthcare software development has enabled the creation of AI systems that give personalized treatment plans. These systems analyze a patient’s hereditary data, way of life, and medical history to prescribe medicines custom-fitted to their particular needs. This approach not only improves the adequacy of medications but also minimizes potential side impacts. For example, custom healthcare software development permits the planning of applications that can anticipate how a patient will react to diverse medicines, ensuring ideal treatment.
Medicine Invention And Development
Generative AI is additionally significant in drug discovery and advancement. By simulating the interaction of atoms with organic systems, AI can recognize potential drug candidates faster than traditional strategies. This approach of telemedicine software accelerates the process of bringing unused medicines to market. Also, EHR software development integrates AI to streamline clinical trials, oversee patient information, and screen adverse impacts, making the development process more productive and successful.
Virtual Health Assistance
Virtual well-being assistants powered by generative AI offer continuous support to patients. These AI-driven chatbots and virtual assistants can oversee appointments, provide restorative data, and offer updates for pharmaceuticals, improving patient adherence to treatment plans. Additionally, with healthcare software development, they can monitor indications and caution healthcare providers in case of any anomalies, ensuring timely mediation.
Top Benefits Of Generative AI In Healthcare
Enhanced Accuracy & Efficiency
Generative AI improves the precision and proficiency of healthcare delivery. Healthcare experts can center on more basic aspects of patient care with healthcare app development by automating scheduled tasks, such as information passage and analysis. AI-driven diagnostic devices decrease the probability of human error, ensuring that patients get precise analysis and suitable medications instantly.
Improved Personalization
Generative AI empowers highly personalized healthcare solutions. By considering a patient’s one-of-a-kind genetic makeup, therapeutic history, and way of life, AI systems can prescribe medicines tailored to individual needs. This personalized approach increases the probability of fruitful results and patient satisfaction.
Cost-effective
Implementing generative AI in healthcare can lead to significant cost savings. By streamlining processes and reducing the requirement for repetitive tests and methods, AI makes a difference and lowers operational costs. Custom healthcare solutions and hospital management software can optimize asset assignment, decreasing waste and improving efficiency.
Enhanced Patient Monitoring and Care
AI-driven systems give persistent observation of patients, particularly those with constant conditions. This custom healthcare software development can track vital signs, analyze patterns, and caution healthcare providers about any changes that require attention. This continuous monitoring improves patient results by empowering timely intercessions.
Transforming the Role Of Healthcare App Development
Healthcare app development enhances individual mobile application experience for health-related matters. It improves executive procedures, improves overall health outcomes, and painless patient care. Using this innovative application, healthcare providers can offer a wide range of services that meet the various needs of patients, caregivers, and medical specialists.
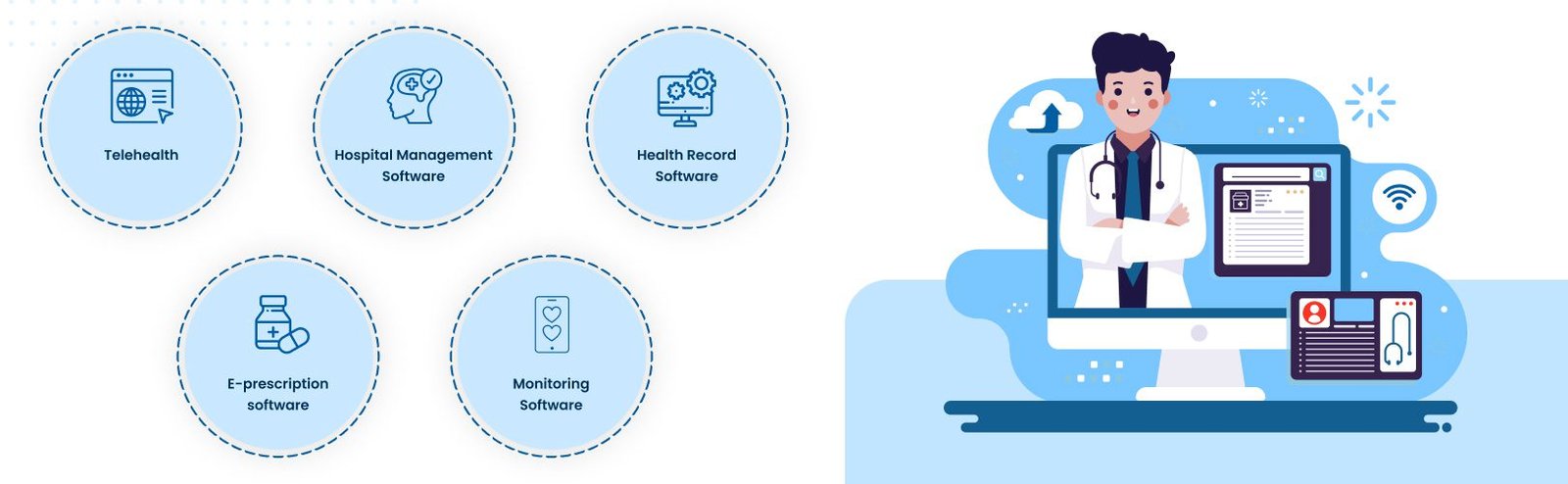
First, telemedicine software made easy appointment scheduling and rapid access to medical information possible. Furthermore, with the assistance of telemedicine software, patients can virtually confer with doctors, receive prescription reminders, and monitor their health metrics on the phone. This user-friendliness increases patient involvement and ensures quick medical response, which may be crucial for treating chronic conditions.
Second, creating healthcare app development facilitates the effective administration of medical facilities. Hospital administration apps automate tasks, including electronic health records (EHR), billing, inventory control, and patient admissions. This automation lessens the workload for healthcare personnel overall, lowers mistakes, and increases their efficiency.
Also, healthcare app development makes a difference in suppliers’ facilitation and communication. Doctors, medical caretakers, and other restorative workforces can work together to create treatment plans, trade understanding information, and keep an eye on patients’ advances in real-time. This coordinated approach ensures that patients urge exhaustive and well-coordinated treatment, which is much appreciated.
Security and protection of information are vital when creating healthcare apps. Engineers are mindful of making beyond any doubt that applications follow laws such as HIPAA to defend private, quiet information. Secure login methods and progressed encryption are fundamental to protecting mystery and certainty.
Creating healthcare apps is essential to updating healthcare delivery and enhancing its efficiency, security, and patient-centeredness. It links patients and healthcare professionals, providing a more responsive and integrated system.
How Does Healthcare App Development Assist the Healthcare Sector?
Data Privacy and Security
One of the essential concerns in healthcare app improvement is ensuring data protection and security. Custom healthcare software improvement must comply with controls such as HIPAA and GDPR to ensure confidential information. AI-driven security systems can distinguish and react to dangers in real time, defending sensitive data.
Accountability and Transparency
AI systems in healthcare must be transparent and responsible. This implies clearly explaining how AI algorithms make decisions and ensuring that these decisions can be audited. Transparency builds belief among healthcare providers and patients, cultivating more extensive acceptance of AI innovations.
Bias and Fairness
Generative AI systems must be designed to avoid biases that could lead to out-of-line treatment. This includes preparing AI models on different datasets and ceaselessly checking their performance. Ensuring fairness in AI-driven healthcare solutions is fundamental to giving equitable care to all patients.
Telemedicine Software to Resolve Future Challenges
Telemedicine software is revolutionizing healthcare, but implementing it will present difficulties, including managing technology infrastructure, protecting patient privacy, and fostering a positive patient-doctor relationship. Data privacy and cybersecurity are critical to the electronic transmission of sensitive patient data.
Furthermore, integrating telemedicine software with current healthcare systems might be expensive and difficult. Patients’ and healthcare professionals’ levels of technological literacy differ as well, creating a learning curve for efficient use. To address these issues and safeguard patient data, sophisticated telemedicine software includes robust encryption and security procedures.
Through seamless integration possibilities with current systems, interoperability, and more seamless transitions are guaranteed. Accessible interfaces and extensive training courses aid in bridging the technical divide and increasing the number of people who can use telemedicine. Telemedicine can potentially improve healthcare delivery as it develops further, providing practical, effective, and safe answers to emerging healthcare problems.
How Generative AI in Healthcare Brings Changes In the Future?
The future of healthcare will be significantly shaped by generative AI – healthcare software development. Advances in AI innovation will lead to more modern diagnostic tools, personalized treatment plans, and efficient medication discovery processes. AI will moreover encourage better patient engagement through virtual well-being colleagues and telemedicine solutions. As healthcare app development advances, we can anticipate more coordinates and user-friendly stages that improve patient care.
Besides, AI-driven clinic management software will optimize operations, from planning to stock management, ensuring that healthcare providers can focus more on persistent care. The continuous change of AI capabilities will drive development, leading to superior healthcare results and more proficient systems.
Bottom Line
Generative AI is introduced in an unused time of persistent care, characterized by upgraded precision, productivity, and personalization. Through healthcare app development and healthcare software development, AI arrangements are becoming more available and compelling. As the healthcare segment proceeds to grasp these advances, patients can see forward to move forward with care and better outcomes. Taking a significant step towards a more efficient, equitable, and patient-focused healthcare system is crucial, as integrating generative AI in healthcare is not only a technological advancement. Are you seeking to develop a healthcare app for your specific needs? EMed HealthTech is here to fulfill your requirements; contact us right away!